SC-200 Practice Exam Free – 50 Questions to Simulate the Real Exam
Are you getting ready for the SC-200 certification? Take your preparation to the next level with our SC-200 Practice Exam Free – a carefully designed set of 50 realistic exam-style questions to help you evaluate your knowledge and boost your confidence.
Using a SC-200 practice exam free is one of the best ways to:
- Experience the format and difficulty of the real exam
- Identify your strengths and focus on weak areas
- Improve your test-taking speed and accuracy
Below, you will find 50 realistic SC-200 practice exam free questions covering key exam topics. Each question reflects the structure and challenge of the actual exam.
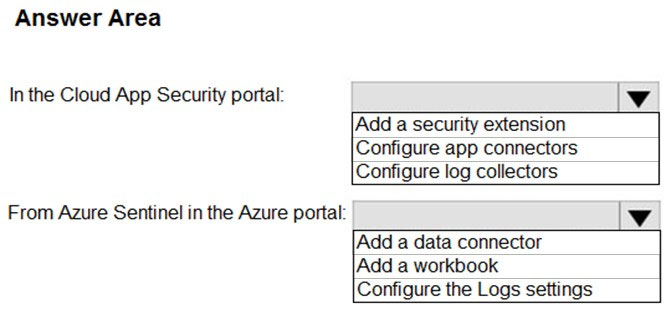
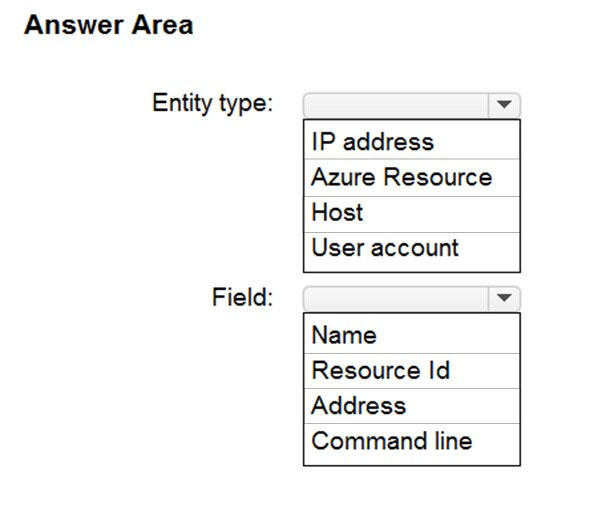
HOTSPOT - You need to configure the Azure Sentinel integration to meet the Azure Sentinel requirements. What should you do? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point. Hot Area:
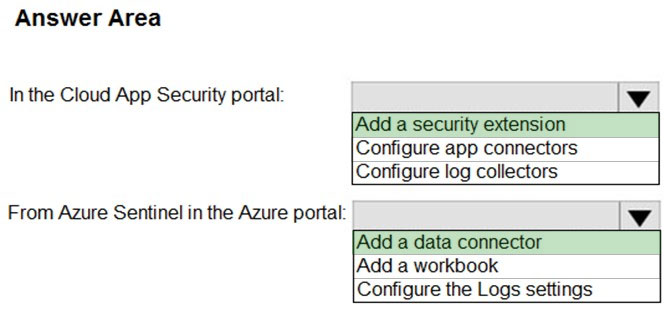
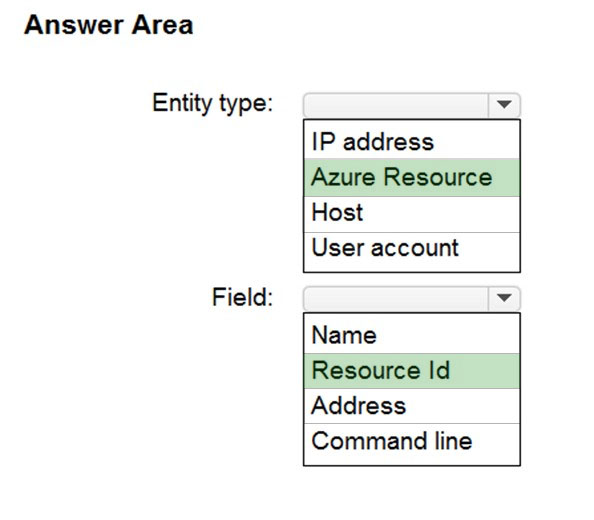
HOTSPOT - You have an Azure Storage account that will be accessed by multiple Azure Function apps during the development of an application. You need to hide Azure Defender alerts for the storage account. Which entity type and field should you use in a suppression rule? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point. Hot Area:
HOTSPOT - You have a Microsoft Sentinel workspace that contains a custom workbook. You need to query for a summary of security events. The solution must meet the following requirements: • Identify the number of security events ingested during the past week. • Display the count of events by day in a chart. How should you complete the query? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.
You have an Azure subscription that uses Microsoft Defender for Servers Plan 1 and contains a server named Server1. You enable agentless scanning. You need to prevent Server1 from being scanned. The solution must minimize administrative effort. What should you do?
A. Create an exclusion tag.
B. Upgrade the subscription to Defender for Servers Plan 2.
C. Create a governance rule.
D. Create an exclusion group.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen. You have an Azure subscription that uses Microsoft Defender XDR. From the Microsoft Defender portal, you perform an audit search and export the results as a file named File1.csv that contains 10,000 rows. You use Microsoft Excel to perform Get & Transform Data operations to parse the AuditData column from File1.csv. The operations fail to generate columns for specific JSON properties. You need to ensure that Excel generates columns for the specific JSON properties in the audit search results. Solution: From Defender, you modify the search criteria of the audit search to reduce the number of returned records, and then you export the results. From Excel, you perform the Get & Transform Data operations by using the new export. Does this meet the requirement?
A. Yes
B. No
DRAG DROP - You have an Azure subscription that contains the users shown in the following table.You need to delegate the following tasks: • Enable Microsoft Defender for Servers on virtual machines. • Review security recommendations and enable server vulnerability scans. The solution must use the principle of least privilege. Which user should perform each task? To answer, drag the appropriate users to the correct tasks. Each user may be used once, more than once, or not at all. You may need to drag the split bar between panes or scroll to view content. NOTE: Each correct selection is worth one point.
You have a Microsoft Sentinel workspace that contains a custom workbook named Workbook1. You need to create a visual based on the SecurityEvent table. The solution must meet the following requirements: • Identify the number of security events ingested during the past week. • Display the count of events by day in a timechart. What should you add to Workbook1?
A. a query
B. a metric
C. a group
D. links or tabs
HOTSPOT - You have an Azure subscription that uses Microsoft Defender for Cloud and contains an Azure logic app named app1. You need to ensure that app1 launches when a specific Defender for Cloud security alert is generated. How should you complete the Azure Resource Manager (ARM) template? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.
You have a Microsoft Sentinel workspace. You investigate an incident that has the following entities: • A user account named User1 • An IP address of 192.168.10.200 • An Azure virtual machine named VM1 • An on-premises server named Server1 You need to label an entity as an indicator of compromise (IoC) directly by using the incidents page. Which entity can you label?
A. 192.168.10.200
B. VM1
C. Server1
D. User1
HOTSPOT - You have a Microsoft 365 subscription that uses Microsoft Defender for Endpoint Plan 2 and contains a Windows device named Device1. You initiated a live response session on Device1. You need to run a command that will download a 250-MB file named File1.exe from the live response library to Device1. The solution must ensure that File1.exe is downloaded as a background process. How should you complete the live response command? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.
HOTSPOT - You have a Microsoft 365 subscription that uses Microsoft Defender for Endpoint Plan 2 and contains a Windows device named Device1. Twenty files on Device1 are quarantined by custom indicators as part of an investigation. You need to release the 20 files from quarantine. How should you complete the command? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.
HOTSPOT - You have a Microsoft 365 E5 subscription that uses Microsoft Defender for Endpoint and contains a Windows device named Device1. You need to investigate a suspicious executable file detected on Device1. The solution must meet the following requirements: • Identify the image file path of the file. • Identify when the file was first detected on Device1. What should you review from the timeline of the detection event? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.
You create a hunting query in Azure Sentinel. You need to receive a notification in the Azure portal as soon as the hunting query detects a match on the query. The solution must minimize effort. What should you use?
A. a playbook
B. a notebook
C. a livestream
D. a bookmark
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen. You are configuring Azure Sentinel. You need to create an incident in Azure Sentinel when a sign-in to an Azure virtual machine from a malicious IP address is detected. Solution: You create a Microsoft incident creation rule for a data connector. Does this meet the goal?
A. Yes
B. No
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen. You are configuring Microsoft Defender for Identity integration with Active Directory. From the Microsoft Defender for identity portal, you need to configure several accounts for attackers to exploit. Solution: From Entity tags, you add the accounts as Honeytoken accounts. Does this meet the goal?
A. Yes
B. No
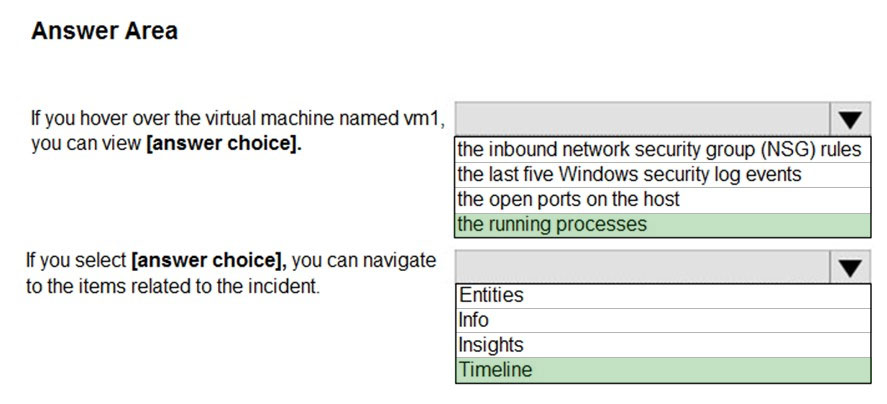
HOTSPOT - From Azure Sentinel, you open the Investigation pane for a high-severity incident as shown in the following exhibit.Use the drop-down menus to select the answer choice that completes each statement based on the information presented in the graphic. NOTE: Each correct selection is worth one point. Hot Area:
You have a Microsoft 365 subscription that contains 1,000 Windows 10 devices. The devices have Microsoft Office 365 installed. You need to mitigate the following device threats: ✑ Microsoft Excel macros that download scripts from untrusted websites ✑ Users that open executable attachments in Microsoft Outlook ✑ Outlook rules and forms exploits What should you use?
A. Microsoft Defender Antivirus
B. attack surface reduction rules in Microsoft Defender for Endpoint
C. Windows Defender Firewall
D. adaptive application control in Azure Defender
You have an Azure subscription that contains a virtual machine named VM1 and uses Azure Defender. Azure Defender has automatic provisioning enabled. You need to create a custom alert suppression rule that will supress false positive alerts for suspicious use of PowerShell on VM1. What should you do first?
A. From Azure Security Center, add a workflow automation.
B. On VM1, run the Get-MPThreatCatalog cmdlet.
C. On VM1 trigger a PowerShell alert.
D. From Azure Security Center, export the alerts to a Log Analytics workspace.
Overview - Fabrikam, Inc. is a financial services company. The company has branch offices in New York, London, and Singapore. Fabrikam has remote users located across the globe. The remote users access company resources, including cloud resources, by using a VPN connection to a branch office. Existing Environment - Identity Environment - The network contains an Active Directory Domain Services (AD DS) forest named fabrikam.com that syncs with an Azure AD tenant named fabrikam.com. To sync the forest, Fabrikam uses Azure AD Connect with pass-through authentication enabled and password hash synchronization disabled. The fabrikam.com forest contains two global groups named Group1 and Group2. Microsoft 365 Environment - All the users at Fabrikam are assigned a Microsoft 365 E5 license and an Azure Active Directory Premium Plan 2 license. Fabrikam implements Microsoft Defender for Identity and Microsoft Defender for Cloud Apps and enables log collectors. Azure Environment - Fabrikam has an Azure subscription that contains the resources shown in the following table.Amazon Web Services (AWS) Environment Fabrikam has an Amazon Web Services (AWS) account named Account1. Account1 contains 100 Amazon Elastic Compute Cloud (EC2) instances that run a custom Windows Server 2022. The image includes Microsoft SQL Server 2019 and does NOT have any agents installed. Current Issues - When the users use the VPN connections, Microsoft 365 Defender raises a high volume of impossible travel alerts that are false positives. Defender for Identity raises a high volume of Suspected DCSync attack alerts that are false positives. Requirements - Planned changes - Fabrikam plans to implement the following services: • Microsoft Defender for Cloud • Microsoft Sentinel Business Requirements - Fabrikam identifies the following business requirements: • Use the principle of least privilege, whenever possible. • Minimize administrative effort. Microsoft Defender for Cloud Apps Requirements Fabrikam identifies the following Microsoft Defender for Cloud Apps requirements: • Ensure that impossible travel alert policies are based on the previous activities of each user. • Reduce the amount of impossible travel alerts that are false positives. Microsoft Defender for Identity Requirements Minimize the administrative effort required to investigate the false positive alerts. Microsoft Defender for Cloud Requirements Fabrikam identifies the following Microsoft Defender for Cloud requirements: • Ensure that the members of Group2 can modify security policies. • Ensure that the members of Group1 can assign regulatory compliance policy initiatives at the Azure subscription level. • Automate the deployment of the Azure Connected Machine agent for Azure Arc-enabled servers to the existing and future resources of Account1. • Minimize the administrative effort required to investigate the false positive alerts. Microsoft Sentinel Requirements - Fabrikam identifies the following Microsoft Sentinel requirements: • Query for NXDOMAIN DNS requests from the last seven days by using built-in Advanced Security Information Model (ASIM) unifying parsers. • From AWS EC2 instances, collect Windows Security event log entries that include local group membership changes. • Identify anomalous activities of Azure AD users by using User and Entity Behavior Analytics (UEBA). • Evaluate the potential impact of compromised Azure AD user credentials by using UEBA. • Ensure that App1 is available for use in Microsoft Sentinel automation rules. • Identify the mean time to triage for incidents generated during the last 30 days. • Identify the mean time to close incidents generated during the last 30 days. • Ensure that the members of Group1 can create and run playbooks. • Ensure that the members of Group1 can manage analytics rules. • Run hunting queries on Pool1 by using Jupyter notebooks. • Ensure that the members of Group2 can manage incidents. • Maximize the performance of data queries. • Minimize the amount of collected data. You need to correlate data from the SecurityEvent Log Analytics table to meet the Microsoft Sentinel requirements for using UEBA. Which Log Analytics table should you use?
A. IdentityInfo
B. AADRiskyUsers
C. SentinelAudit
D. IdentityDirectoryEvents
You have an Azure subscription that uses Microsoft Sentinel and contains 100 Linux virtual machines. You need to monitor the virtual machines by using Microsoft Sentinel. The solution must meet the following requirements: ✑ Minimize administrative effort. ✑ Minimize the parsing required to read fog data. What should you configure?
A. a Log Analytics Data Collector API
B. REST API integration
C. a Common Evert Format (CEF) connector
D. a Syslog connector
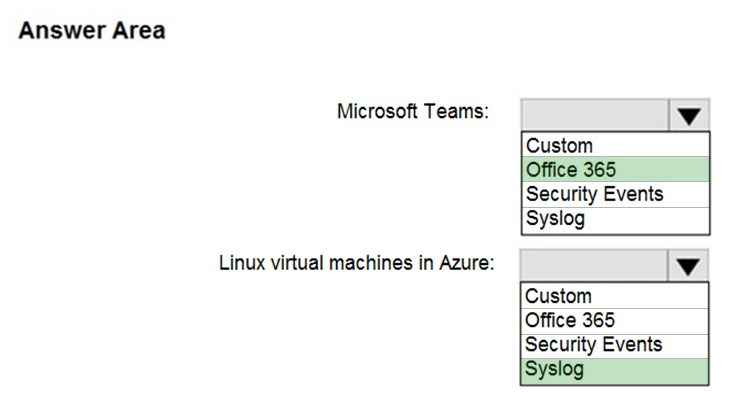
HOTSPOT - You deploy Azure Sentinel. You need to implement connectors in Azure Sentinel to monitor Microsoft Teams and Linux virtual machines in Azure. The solution must minimize administrative effort. Which data connector type should you use for each workload? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point. Hot Area:
You have an Azure subscription that uses Microsoft Defender for Cloud and contains 100 virtual machines that run Windows Server. You need to configure Defender for Cloud to collect event data from the virtual machines. The solution must minimize administrative effort and costs. Which two actions should you perform? Each correct answer presents part of the solution. NOTE: Each correct selection is worth one point.
A. From the workspace created by Defender for Cloud, set the data collection level to Common.
B. From the Microsoft Endpoint Manager admin center, enable automatic enrollment.
C. From the Azure portal, create an Azure Event Grid subscription.
D. From the workspace created by Defender for Cloud, set the data collection level to All Events.
E. From Defender for Cloud in the Azure portal, enable automatic provisioning for the virtual machines.
You have a Microsoft 365 E5 subscription that uses Microsoft SharePoint Online. You delete users from the subscription. You need to be notified if the deleted users downloaded numerous documents from SharePoint Online sites during the month before their accounts were deleted. What should you use?
A. a file policy in Microsoft Defender for Cloud Apps
B. an access review policy
C. an alert policy in Microsoft Defender for Office 365
D. an insider risk policy
You have a custom analytics rule to detect threats in Azure Sentinel. You discover that the analytics rule stopped running. The rule was disabled, and the rule name has a prefix of AUTO DISABLED. What is a possible cause of the issue?
A. There are connectivity issues between the data sources and Log Analytics.
B. The number of alerts exceeded 10,000 within two minutes.
C. The rule query takes too long to run and times out.
D. Permissions to one of the data sources of the rule query were modified.
DRAG DROP - Overview - Fabrikam, Inc. is a financial services company. The company has branch offices in New York, London, and Singapore. Fabrikam has remote users located across the globe. The remote users access company resources, including cloud resources, by using a VPN connection to a branch office. Existing Environment - Identity Environment - The network contains an Active Directory Domain Services (AD DS) forest named fabrikam.com that syncs with an Azure AD tenant named fabrikam.com. To sync the forest, Fabrikam uses Azure AD Connect with pass-through authentication enabled and password hash synchronization disabled. The fabrikam.com forest contains two global groups named Group1 and Group2. Microsoft 365 Environment - All the users at Fabrikam are assigned a Microsoft 365 E5 license and an Azure Active Directory Premium Plan 2 license. Fabrikam implements Microsoft Defender for Identity and Microsoft Defender for Cloud Apps and enables log collectors. Azure Environment - Fabrikam has an Azure subscription that contains the resources shown in the following table.Amazon Web Services (AWS) Environment Fabrikam has an Amazon Web Services (AWS) account named Account1. Account1 contains 100 Amazon Elastic Compute Cloud (EC2) instances that run a custom Windows Server 2022. The image includes Microsoft SQL Server 2019 and does NOT have any agents installed. Current Issues - When the users use the VPN connections, Microsoft 365 Defender raises a high volume of impossible travel alerts that are false positives. Defender for Identity raises a high volume of Suspected DCSync attack alerts that are false positives. Requirements - Planned changes - Fabrikam plans to implement the following services: • Microsoft Defender for Cloud • Microsoft Sentinel Business Requirements - Fabrikam identifies the following business requirements: • Use the principle of least privilege, whenever possible. • Minimize administrative effort. Microsoft Defender for Cloud Apps Requirements Fabrikam identifies the following Microsoft Defender for Cloud Apps requirements: • Ensure that impossible travel alert policies are based on the previous activities of each user. • Reduce the amount of impossible travel alerts that are false positives. Microsoft Defender for Identity Requirements Minimize the administrative effort required to investigate the false positive alerts. Microsoft Defender for Cloud Requirements Fabrikam identifies the following Microsoft Defender for Cloud requirements: • Ensure that the members of Group2 can modify security policies. • Ensure that the members of Group1 can assign regulatory compliance policy initiatives at the Azure subscription level. • Automate the deployment of the Azure Connected Machine agent for Azure Arc-enabled servers to the existing and future resources of Account1. • Minimize the administrative effort required to investigate the false positive alerts. Microsoft Sentinel Requirements Fabrikam identifies the following Microsoft Sentinel requirements: • Query for NXDOMAIN DNS requests from the last seven days by using built-in Advanced Security Information Model (ASIM) unifying parsers. • From AWS EC2 instances, collect Windows Security event log entries that include local group membership changes. • Identify anomalous activities of Azure AD users by using User and Entity Behavior Analytics (UEBA). • Evaluate the potential impact of compromised Azure AD user credentials by using UEBA. • Ensure that App1 is available for use in Microsoft Sentinel automation rules. • Identify the mean time to triage for incidents generated during the last 30 days. • Identify the mean time to close incidents generated during the last 30 days. • Ensure that the members of Group1 can create and run playbooks. • Ensure that the members of Group1 can manage analytics rules. • Run hunting queries on Pool1 by using Jupyter notebooks. • Ensure that the members of Group2 can manage incidents. • Maximize the performance of data queries. • Minimize the amount of collected data. You need to assign role-based access control (RBAC) roles to Group1 and Group2 to meet the Microsoft Sentinel requirements and the business requirements. Which role should you assign to each group? To answer, drag the appropriate roles to the correct groups. Each role may be used once, more than once, or not at all. You may need to drag the split bar between panes or scroll to view content. NOTE: Each correct selection is worth one point.
You implement Safe Attachments policies in Microsoft Defender for Office 365. Users report that email messages containing attachments take longer than expected to be received. You need to reduce the amount of time it takes to deliver messages that contain attachments without compromising security. The attachments must be scanned for malware, and any messages that contain malware must be blocked. What should you configure in the Safe Attachments policies?
A. Dynamic Delivery
B. Replace
C. Block and Enable redirect
D. Monitor and Enable redirect
Overview - Fabrikam, Inc. is a financial services company. The company has branch offices in New York, London, and Singapore. Fabrikam has remote users located across the globe. The remote users access company resources, including cloud resources, by using a VPN connection to a branch office. Existing Environment - Identity Environment - The network contains an Active Directory Domain Services (AD DS) forest named fabrikam.com that syncs with an Azure AD tenant named fabrikam.com. To sync the forest, Fabrikam uses Azure AD Connect with pass-through authentication enabled and password hash synchronization disabled. The fabrikam.com forest contains two global groups named Group1 and Group2. Microsoft 365 Environment - All the users at Fabrikam are assigned a Microsoft 365 E5 license and an Azure Active Directory Premium Plan 2 license. Fabrikam implements Microsoft Defender for Identity and Microsoft Defender for Cloud Apps and enables log collectors. Azure Environment - Fabrikam has an Azure subscription that contains the resources shown in the following table.Amazon Web Services (AWS) Environment Fabrikam has an Amazon Web Services (AWS) account named Account1. Account1 contains 100 Amazon Elastic Compute Cloud (EC2) instances that run a custom Windows Server 2022. The image includes Microsoft SQL Server 2019 and does NOT have any agents installed. Current Issues - When the users use the VPN connections, Microsoft 365 Defender raises a high volume of impossible travel alerts that are false positives. Defender for Identity raises a high volume of Suspected DCSync attack alerts that are false positives. Requirements - Planned changes - Fabrikam plans to implement the following services: • Microsoft Defender for Cloud • Microsoft Sentinel Business Requirements - Fabrikam identifies the following business requirements: • Use the principle of least privilege, whenever possible. • Minimize administrative effort. Microsoft Defender for Cloud Apps Requirements Fabrikam identifies the following Microsoft Defender for Cloud Apps requirements: • Ensure that impossible travel alert policies are based on the previous activities of each user. • Reduce the amount of impossible travel alerts that are false positives. Microsoft Defender for Identity Requirements Minimize the administrative effort required to investigate the false positive alerts. Microsoft Defender for Cloud Requirements Fabrikam identifies the following Microsoft Defender for Cloud requirements: • Ensure that the members of Group2 can modify security policies. • Ensure that the members of Group1 can assign regulatory compliance policy initiatives at the Azure subscription level. • Automate the deployment of the Azure Connected Machine agent for Azure Arc-enabled servers to the existing and future resources of Account1. • Minimize the administrative effort required to investigate the false positive alerts. Microsoft Sentinel Requirements - Fabrikam identifies the following Microsoft Sentinel requirements: • Query for NXDOMAIN DNS requests from the last seven days by using built-in Advanced Security Information Model (ASIM) unifying parsers. • From AWS EC2 instances, collect Windows Security event log entries that include local group membership changes. • Identify anomalous activities of Azure AD users by using User and Entity Behavior Analytics (UEBA). • Evaluate the potential impact of compromised Azure AD user credentials by using UEBA. • Ensure that App1 is available for use in Microsoft Sentinel automation rules. • Identify the mean time to triage for incidents generated during the last 30 days. • Identify the mean time to close incidents generated during the last 30 days. • Ensure that the members of Group1 can create and run playbooks. • Ensure that the members of Group1 can manage analytics rules. • Run hunting queries on Pool1 by using Jupyter notebooks. • Ensure that the members of Group2 can manage incidents. • Maximize the performance of data queries. • Minimize the amount of collected data. You need to meet the Microsoft Sentinel requirements for App1. What should you configure for App1?
A. a trigger
B. a connector
C. authorization
D. an API connection
You have a Microsoft Sentinel workspace. You need to identify which rules are used to detect advanced multistage attacks that comprise two or more alerts or activities. The solution must minimize administrative effort. Which rule type should you query?
A. Fusion
B. Microsoft Security
C. ML Behavior Analytics
D. Scheduled
You have an Azure subscription that has the enhanced security features in Microsoft Defender for Cloud enabled and contains a user named User1. You need to ensure that User1 can export alert data from Defender for Cloud. The solution must use the principle of least privilege. Which role should you assign to User1?
A. User Access Administrator
B. Owner
C. Contributor
D. Reader
You create an Azure subscription. You enable Azure Defender for the subscription. You need to use Azure Defender to protect on-premises computers. What should you do on the on-premises computers?
A. Install the Log Analytics agent.
B. Install the Dependency agent.
C. Configure the Hybrid Runbook Worker role.
D. Install the Connected Machine agent.
HOTSPOT - You have a Microsoft Sentinel workspace that contains a custom workbook named Workbook1. You need to create a visual in Workbook1 that will display the logon count for accounts that have logon event IDs of 4624 and 4634. How should you complete the query? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.
HOTSPOT - You have a Microsoft 365 subscription that uses Microsoft Purview and contains a Microsoft SharePoint Online site named Site1. Site1 contains the files shown in the following table.From Microsoft Purview, you create the content search queries shown in the following table.
For each of the following statements, select Yes if the statement is true. Otherwise, select No. NOTE: Each correct selection is worth one point.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen. You have Linux virtual machines on Amazon Web Services (AWS). You deploy Azure Defender and enable auto-provisioning. You need to monitor the virtual machines by using Azure Defender. Solution: You manually install the Log Analytics agent on the virtual machines. Does this meet the goal?
A. Yes
B. No
You have a Microsoft 365 subscription that uses Microsoft Defender XDR. You are investigating an attacker that is known to use the Microsoft Graph API as an attack vector. The attacker performs the tactics shown the following table.You need to search for malicious activities in your organization. Which tactics can you analyze by using the MicrosoftGraphActivityLogs table?
A. Tactic2 only
B. Tactic1 and Tactic2 only
C. Tactic2 and Tactic3 only
D. Tactic1, Tactic2, and Tactic3
You have a Microsoft Sentinel workspace. You enable User and Entity Behavior Analytics (UEBA) by using Audit Logs and Signin Logs. The following entities are detected in the Azure AD tenant: • App name: App1 • IP address: 192.168.1.2 • Computer name: Device1 • Used client app: Microsoft Edge • Email address: user1@company.com • Sign-in URL: https://www.company.com Which entities can be investigated by using UEBA?
A. IP address and email address only
B. app name, computer name, IP address, email address, and used client app only
C. IP address only
D. used client app and app name only
You have a Microsoft 365 subscription that uses Microsoft Defender XDR. You are investigating an attacker that is known to use the Microsoft Graph API as an attack vector. The attacker performs the tactics shown the following table.You need to search for malicious activities in your organization. Which tactics can you analyze by using the MicrosoftGraphActivityLogs table?
A. Tactic1 only
B. Tactic2 only
C. Tactic1 and Tactic3 only
D. Tactic2 and Tactic3 only
E. Tactic1, Tactic2, and Tactic3
You use Azure Defender. You have an Azure Storage account that contains sensitive information. You need to run a PowerShell script if someone accesses the storage account from a suspicious IP address. Which two actions should you perform? Each correct answer presents part of the solution. NOTE: Each correct selection is worth one point.
A. From Azure Security Center, enable workflow automation.
B. Create an Azure logic app that has a manual trigger.
C. Create an Azure logic app that has an Azure Security Center alert trigger.
D. Create an Azure logic app that has an HTTP trigger.
E. From Azure Active Directory (Azure AD), add an app registration.
DRAG DROP - You have 50 on-premises servers. You have an Azure subscription that uses Microsoft Defender for Cloud. The Defender for Cloud deployment has Microsoft Defender for Servers and automatic provisioning enabled. You need to configure Defender for Cloud to support the on-premises servers. The solution must meet the following requirements: • Provide threat and vulnerability management. • Support data collection rules. Which three actions should you perform in sequence? To answer, move the appropriate actions from the list of actions to the answer area and arrange them in the correct order.
You have a Microsoft 365 subscription that uses Microsoft Defender for Endpoint Plan 2 and contains 500 Windows devices. You plan to create a Microsoft Defender XDR custom deception rule. You need to ensure that the rule will be applied to only 10 specific devices. What should you do first?
A. Add custom lures to the rule.
B. Add the IP address of each device to the list of decoy accounts and hosts of the rule.
C. Add the devices to a group.
D. Assign a tag to the devices.
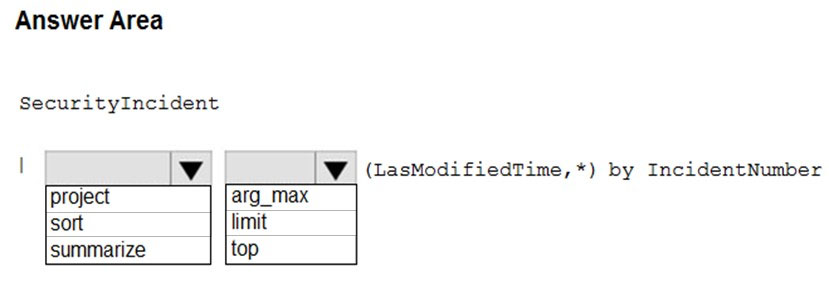
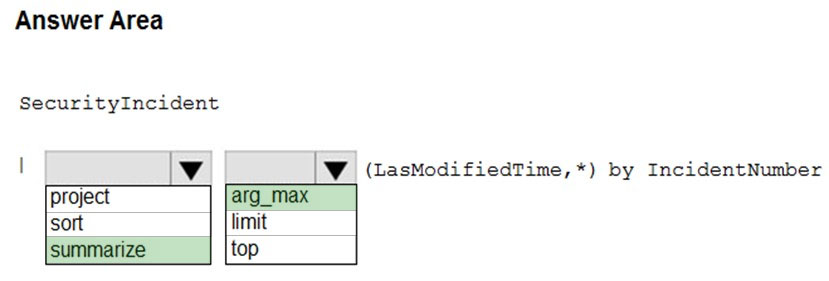
HOTSPOT - You need to create a query for a workbook. The query must meet the following requirements: ✑ List all incidents by incident number. ✑ Only include the most recent log for each incident. How should you complete the query? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point. Hot Area:
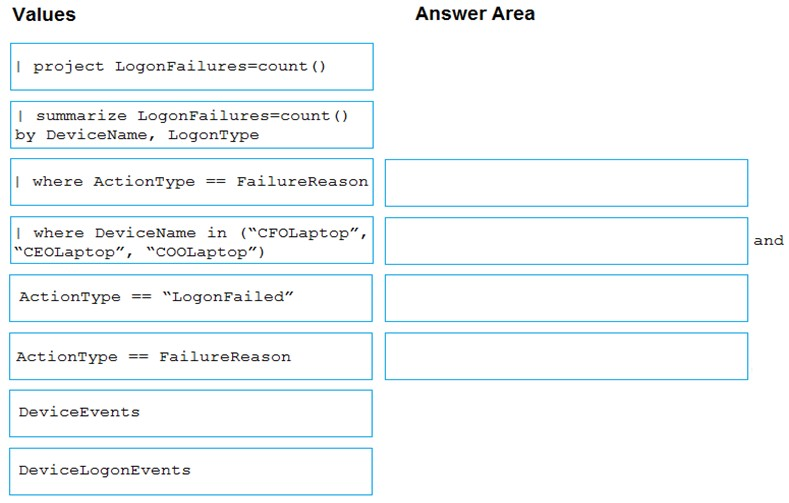
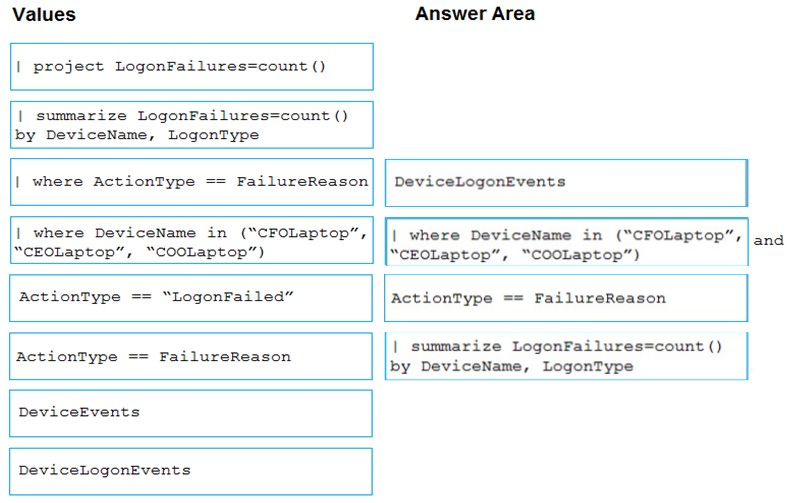
DRAG DROP - You are investigating an incident by using Microsoft 365 Defender. You need to create an advanced hunting query to count failed sign-in authentications on three devices named CFOLaptop, CEOLaptop, and COOLaptop. How should you complete the query? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point. Select and Place:
Overview - Fabrikam, Inc. is a financial services company. The company has branch offices in New York, London, and Singapore. Fabrikam has remote users located across the globe. The remote users access company resources, including cloud resources, by using a VPN connection to a branch office. Existing Environment - Identity Environment - The network contains an Active Directory Domain Services (AD DS) forest named fabrikam.com that syncs with an Azure AD tenant named fabrikam.com. To sync the forest, Fabrikam uses Azure AD Connect with pass-through authentication enabled and password hash synchronization disabled. The fabrikam.com forest contains two global groups named Group1 and Group2. Microsoft 365 Environment - All the users at Fabrikam are assigned a Microsoft 365 E5 license and an Azure Active Directory Premium Plan 2 license. Fabrikam implements Microsoft Defender for Identity and Microsoft Defender for Cloud Apps and enables log collectors. Azure Environment - Fabrikam has an Azure subscription that contains the resources shown in the following table.Amazon Web Services (AWS) Environment Fabrikam has an Amazon Web Services (AWS) account named Account1. Account1 contains 100 Amazon Elastic Compute Cloud (EC2) instances that run a custom Windows Server 2022. The image includes Microsoft SQL Server 2019 and does NOT have any agents installed. Current Issues - When the users use the VPN connections, Microsoft 365 Defender raises a high volume of impossible travel alerts that are false positives. Defender for Identity raises a high volume of Suspected DCSync attack alerts that are false positives. Requirements - Planned changes - Fabrikam plans to implement the following services: • Microsoft Defender for Cloud • Microsoft Sentinel Business Requirements - Fabrikam identifies the following business requirements: • Use the principle of least privilege, whenever possible. • Minimize administrative effort. Microsoft Defender for Cloud Apps Requirements Fabrikam identifies the following Microsoft Defender for Cloud Apps requirements: • Ensure that impossible travel alert policies are based on the previous activities of each user. • Reduce the amount of impossible travel alerts that are false positives. Microsoft Defender for Identity Requirements Minimize the administrative effort required to investigate the false positive alerts. Microsoft Defender for Cloud Requirements Fabrikam identifies the following Microsoft Defender for Cloud requirements: • Ensure that the members of Group2 can modify security policies. • Ensure that the members of Group1 can assign regulatory compliance policy initiatives at the Azure subscription level. • Automate the deployment of the Azure Connected Machine agent for Azure Arc-enabled servers to the existing and future resources of Account1. • Minimize the administrative effort required to investigate the false positive alerts. Microsoft Sentinel Requirements - Fabrikam identifies the following Microsoft Sentinel requirements: • Query for NXDOMAIN DNS requests from the last seven days by using built-in Advanced Security Information Model (ASIM) unifying parsers. • From AWS EC2 instances, collect Windows Security event log entries that include local group membership changes. • Identify anomalous activities of Azure AD users by using User and Entity Behavior Analytics (UEBA). • Evaluate the potential impact of compromised Azure AD user credentials by using UEBA. • Ensure that App1 is available for use in Microsoft Sentinel automation rules. • Identify the mean time to triage for incidents generated during the last 30 days. • Identify the mean time to close incidents generated during the last 30 days. • Ensure that the members of Group1 can create and run playbooks. • Ensure that the members of Group1 can manage analytics rules. • Run hunting queries on Pool1 by using Jupyter notebooks. • Ensure that the members of Group2 can manage incidents. • Maximize the performance of data queries. • Minimize the amount of collected data. You need to minimize the effort required to investigate the Microsoft Defender for Identity false positive alerts. What should you review?
A. the status update time
B. the resolution method of the source computer
C. the alert status
D. the certainty of the source computer
Overview - Fabrikam, Inc. is a financial services company. The company has branch offices in New York, London, and Singapore. Fabrikam has remote users located across the globe. The remote users access company resources, including cloud resources, by using a VPN connection to a branch office. Existing Environment - Identity Environment - The network contains an Active Directory Domain Services (AD DS) forest named fabrikam.com that syncs with an Azure AD tenant named fabrikam.com. To sync the forest, Fabrikam uses Azure AD Connect with pass-through authentication enabled and password hash synchronization disabled. The fabrikam.com forest contains two global groups named Group1 and Group2. Microsoft 365 Environment - All the users at Fabrikam are assigned a Microsoft 365 E5 license and an Azure Active Directory Premium Plan 2 license. Fabrikam implements Microsoft Defender for Identity and Microsoft Defender for Cloud Apps and enables log collectors. Azure Environment - Fabrikam has an Azure subscription that contains the resources shown in the following table.Amazon Web Services (AWS) Environment Fabrikam has an Amazon Web Services (AWS) account named Account1. Account1 contains 100 Amazon Elastic Compute Cloud (EC2) instances that run a custom Windows Server 2022. The image includes Microsoft SQL Server 2019 and does NOT have any agents installed. Current Issues - When the users use the VPN connections, Microsoft 365 Defender raises a high volume of impossible travel alerts that are false positives. Defender for Identity raises a high volume of Suspected DCSync attack alerts that are false positives. Requirements - Planned changes - Fabrikam plans to implement the following services: • Microsoft Defender for Cloud • Microsoft Sentinel Business Requirements - Fabrikam identifies the following business requirements: • Use the principle of least privilege, whenever possible. • Minimize administrative effort. Microsoft Defender for Cloud Apps Requirements Fabrikam identifies the following Microsoft Defender for Cloud Apps requirements: • Ensure that impossible travel alert policies are based on the previous activities of each user. • Reduce the amount of impossible travel alerts that are false positives. Microsoft Defender for Identity Requirements Minimize the administrative effort required to investigate the false positive alerts. Microsoft Defender for Cloud Requirements Fabrikam identifies the following Microsoft Defender for Cloud requirements: • Ensure that the members of Group2 can modify security policies. • Ensure that the members of Group1 can assign regulatory compliance policy initiatives at the Azure subscription level. • Automate the deployment of the Azure Connected Machine agent for Azure Arc-enabled servers to the existing and future resources of Account1. • Minimize the administrative effort required to investigate the false positive alerts. Microsoft Sentinel Requirements - Fabrikam identifies the following Microsoft Sentinel requirements: • Query for NXDOMAIN DNS requests from the last seven days by using built-in Advanced Security Information Model (ASIM) unifying parsers. • From AWS EC2 instances, collect Windows Security event log entries that include local group membership changes. • Identify anomalous activities of Azure AD users by using User and Entity Behavior Analytics (UEBA). • Evaluate the potential impact of compromised Azure AD user credentials by using UEBA. • Ensure that App1 is available for use in Microsoft Sentinel automation rules. • Identify the mean time to triage for incidents generated during the last 30 days. • Identify the mean time to close incidents generated during the last 30 days. • Ensure that the members of Group1 can create and run playbooks. • Ensure that the members of Group1 can manage analytics rules. • Run hunting queries on Pool1 by using Jupyter notebooks. • Ensure that the members of Group2 can manage incidents. • Maximize the performance of data queries. • Minimize the amount of collected data. You need to ensure that you can run hunting queries to meet the Microsoft Sentinel requirements. Which type of workspace should you create?
A. Azure Synapse Analytics
B. Azure Machine Learning
C. Log Analytics
D. Azure Databricks
HOTSPOT - Overview - Adatum Corporation is a United States-based financial services company that has regional offices in New York, Chicago, and San Francisco. Existing Environment - Identity Environment - The on-premises network contains an Active Directory Domain Services (AD DS) forest named corp.adatum.com that syncs with an Azure AD tenant named adatum.com. All user and group management tasks are performed in corp.adatum.com. The corp.adatum.com domain contains a group named Group1 that syncs with adatum.com. Licensing Status - All the users at Adatum are assigned a Microsoft 365 ES license and an Azure Active Directory Premium P2 license. Cloud Environment - The cloud environment contains a Microsoft 365 subscription, an Azure subscription linked to the adatum.com tenant, and the resources shown in the following table.On-premises Environment - The on-premises network contains the resources shown in the following table.
Requirements - Planned changes - Adatum plans to perform the following changes: • Implement a query named rulequery1 that will include the following KQL query.
• Implement a Microsoft Sentinel scheduled rule that generates incidents based on rulequery1. Microsoft Defender for Cloud Requirements Adatum identifies the following Microsoft Defender for Cloud requirements: • The members of Group1 must be able to enable Defender for Cloud plans and apply regulatory compliance initiatives. • Microsoft Defender for Servers Plan 2 must be enabled on all the Azure virtual machines. • Server2 must be excluded from agentless scanning. Microsoft Sentinel Requirements Adatum identifies the following Microsoft Sentinel requirements: • Implement an Advanced Security Information Model (ASIM) query that will return a count of DNS requests that results in an NXDOMAIN response from Infoblox1. • Ensure that multiple alerts generated by rulequery1 in response to a single user launching Azure Cloud Shell multiple times are consolidated as a single incident. • Implement the Windows Security Events via AMA connector for Microsoft Sentinel and configure it to monitor the Security event log of Server1. • Ensure that incidents generated by rulequery1 are closed automatically if Azure Cloud Shell is launched by the company’s SecOps team. • Implement a custom Microsoft Sentinel workbook named Workbook1 that will include a query to dynamically retrieve data from Webapp1. • Implement a Microsoft Sentinel near-real-time (NRT) analytics rule that detects sign-ins to a designated break glass account. • Ensure that HuntingQuery1 runs automatically when the Hunting page of Microsoft Sentinel in the Azure portal is accessed. • Ensure that higher than normal volumes of password resets for corp.adatum.com user accounts are detected. • Minimize the overhead associated with queries that use ASIM parsers. • Ensure that the Group1 members can create and edit playbooks. • Use built-in ASIM parsers whenever possible. Business Requirements - Adatum identifies the following business requirements: • Follow the principle of least privilege whenever possible. • Minimize administrative effort whenever possible. You need to implement the Microsoft Sentinel NRT rule for monitoring the designated break glass account. The solution must meet the Microsoft Sentinel requirements. How should you complete the query? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.
You have a Microsoft 365 subscription that uses Microsoft Defender for Endpoint. You need to add threat indicators for all the IP addresses in a range of 171.23.34.32-171.23.34.63. The solution must minimize administrative effort. What should you do in the Microsoft 365 Defender portal?
A. Create an import file that contains the individual IP addresses in the range. Select Import and import the file.
B. Create an import file that contains the IP address of 171.23.34.32/27. Select Import and import the file.
C. Select Add indicator and set the IP address to 171.23.34.32-171.23.34.63.
D. Select Add indicator and set the IP address to 171.23.34.32/27.
You have an Azure subscription that contains a user named User1. User1 is assigned an Azure Active Directory Premium Plan 2 license. You need to identify whether the identity of User1 was compromised during the last 90 days. What should you use?
A. the risk detections report
B. the risky users report
C. Identity Secure Score recommendations
D. the risky sign-ins report
You have a Microsoft 365 E5 subscription that is linked to a hybrid Azure AD tenant. You need to identify all the changes made to Domain Admins group during the past 30 days. What should you use?
A. the Modifications of sensitive groups report in Microsoft Defender for Identity
B. the identity security posture assessment in Microsoft Defender for Cloud Apps
C. the Azure Active Directory Provisioning Analysis workbook
D. the Overview settings of Insider risk management
You have a Microsoft 365 subscription that uses Microsoft 365 Defender. You plan to create a hunting query from Microsoft Defender. You need to create a custom tracked query that will be used to assess the threat status of the subscription. From the Microsoft 365 Defender portal, which page should you use to create the query?
A. Threat analytics
B. Advanced Hunting
C. Explorer
D. Policies & rules
HOTSPOT - You have the following KQL query.For each of the following statements, select Yes if the statement is true. Otherwise. select No. NOTE: Each correct selection is worth one point.
You have an Azure subscription that contains a user named User1 and a Microsoft Sentinel workspace named WS1. WS1 uses Microsoft Defender for Cloud. You have the Microsoft security analytics rules shown in the following table.User1 performs an action that matches Rule1, Rule2, Rule3, and Rule4. How many incidents will be created in WS1?
A. 1
B. 2
C. 3
D. 4
Free Access Full SC-200 Practice Exam Free
Looking for additional practice? Click here to access a full set of SC-200 practice exam free questions and continue building your skills across all exam domains.
Our question sets are updated regularly to ensure they stay aligned with the latest exam objectives—so be sure to visit often!
Good luck with your SC-200 certification journey!